D365Hub
Your learning hub for Microsoft Dynamics 365, Power Platform and related technologies
Popular posts
-
Power Virtual Agents: Creating adaptive cards with... If you're a Power Virtual Agents user, this article provides a tutorial on creating adaptive cards w...
-
How to Disable Copilot in Dynamics 365 CE | User G... Copilot is a popular and powerful feature in Dynamics 365 Customer Engagement that offers assistance...
-
D365 F&O - Create custom workflow in Dynamics 365 This guide will explain every step needed to create your custom workflow in Dynamics 365. Create ...
-
Create Generative AI solutions with Power Virtual ... If you're looking to integrate generative AI solutions into your business operations, the integratio...
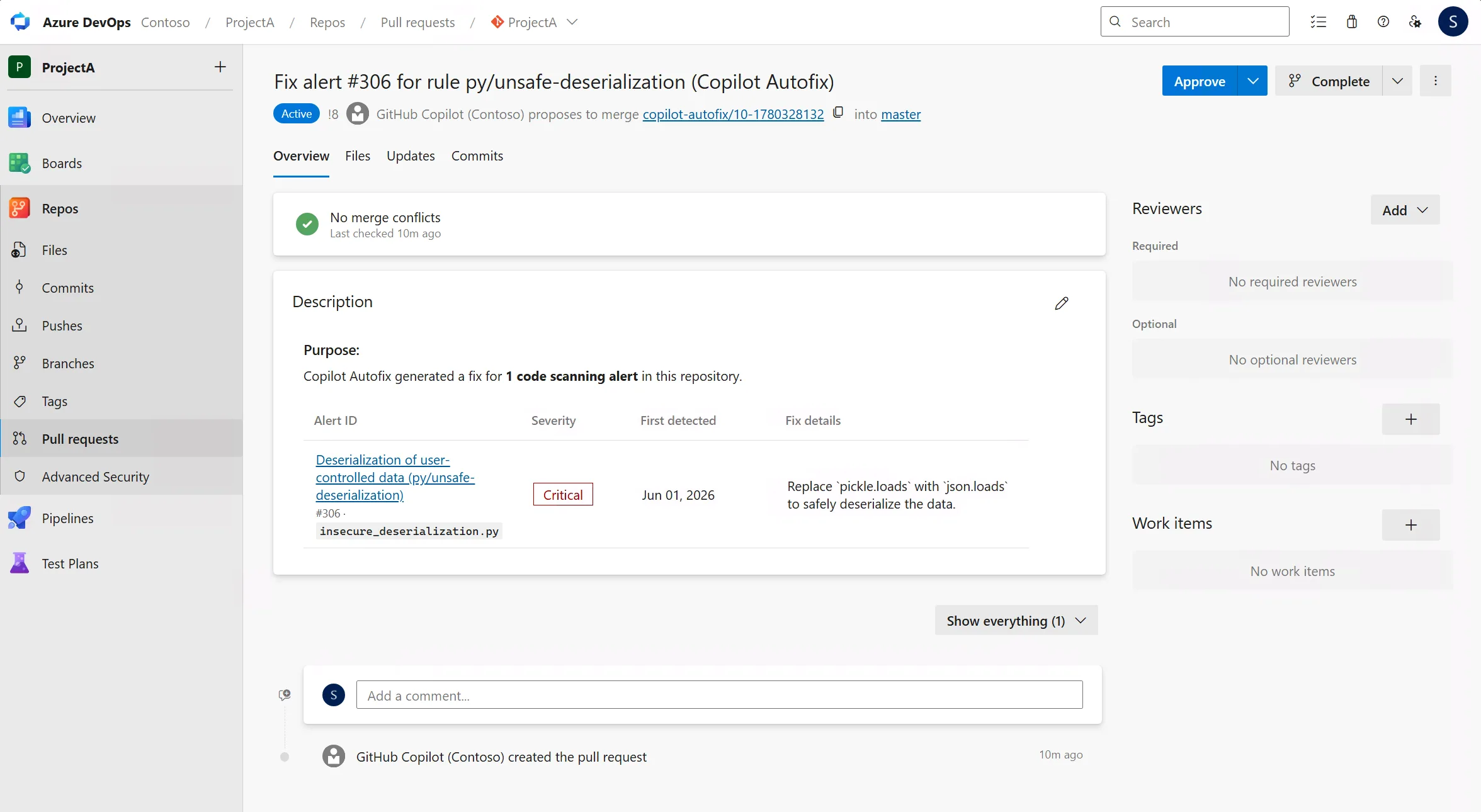
Copilot Autofix for GitHub Advanced Security ...
Over the last few years, we’ve encouraged customers to move their repositories from ...

Office 365 Outlook Get Attachment
Fetches a single email attachment by its ID, returning its name, type, size, and base64 co...

Fix invalid Microsoft service API permissions...
Learn how to fix invalid Microsoft service API permissions in SharePoint and ensure smooth...

Primer: Finding Sensitivity Labels with Power...
Three cmdlets exist to fetch sensitivity labels. One is in the Exchange Online module; the...

Introducing Corvus.Text.Json V5: Pooled-Memor...
ParsedJsonDocument uses ArrayPool-backed memory for just 136 bytes of GC pressure per docu...

Agents League Hackathon 2026 – Enterprise Age...
From declarative agents for Microsoft 365 Copilot to fully autonomous multi-agent systems ...

Dataverse Business Skills: Teaching Your Agen...
The Problem Nobody Talks About You’ve connected your agent to Dataverse. It can quer...

Week 11 Updates : Free Microsoft Dynamics 365...
11 weeks in. 58 videos published. Still free. This week — we closed Fixed Assets. And brou...

Microsoft Dynamics 365 vs Salesforce: A Pract...
In many organizations currently using Salesforce, the friction does not initially feel lik...
How to Perform CRUD Operations in Microsoft D...
In modern enterprise applications, integrating external systems with Microsoft Dataverse h...

Agent 365 | Identity & Access Controls in Ent...
Take control of every AI agent, managed or not, running in your environment using Agent 36...

Episode 429: Getting started with LLM Wikis
Welcome to Episode 429 of the Microsoft Cloud IT Pro Podcast. In this episode, Scott and B...

Introducing Azure HorizonDB - PostgreSQL
Run enterprise Postgres workloads on Azure HorizonDB with around 3x the throughput of self...

Agent 365 | Security Operations in Defender
Surface every AI agent in your tenant and expose the ones throwing security signals — acro...

Microsoft Entra Tenant Governance | Find Conf...
Ensure your tenant configuration doesn't drift from defined security and compliance requir...

Episode 428: Migrating Group Policy to Micros...
Welcome to Episode 428 of the Microsoft Cloud IT Pro Podcast. In this episode, Ben and Sco...

Automate evaluations | Microsoft Foundry
Build AI agents that meet your standards for quality, safety, and performance using Micros...

Microsoft Excel Beginners Tutorial (2026)
This is the Microsoft Excel guide and tutorial for beginners. If you're new to and getting...

Work IQ | Data, Context, Skills & Tools for C...
Ground every Microsoft 365 Copilot response in your real work data. Pull context from Shar...









































