How to Create Azure AD Security Group using Microsoft Graph APIs (Postman & Python Code Sample)
Azure Active Directory (Azure AD) groups are used to manage users that all need the same access and permissions to resources, such as potentially restricted apps and services. Instead of adding special permissions to individual users, you create a group that applies the special permissions to every member of that group.
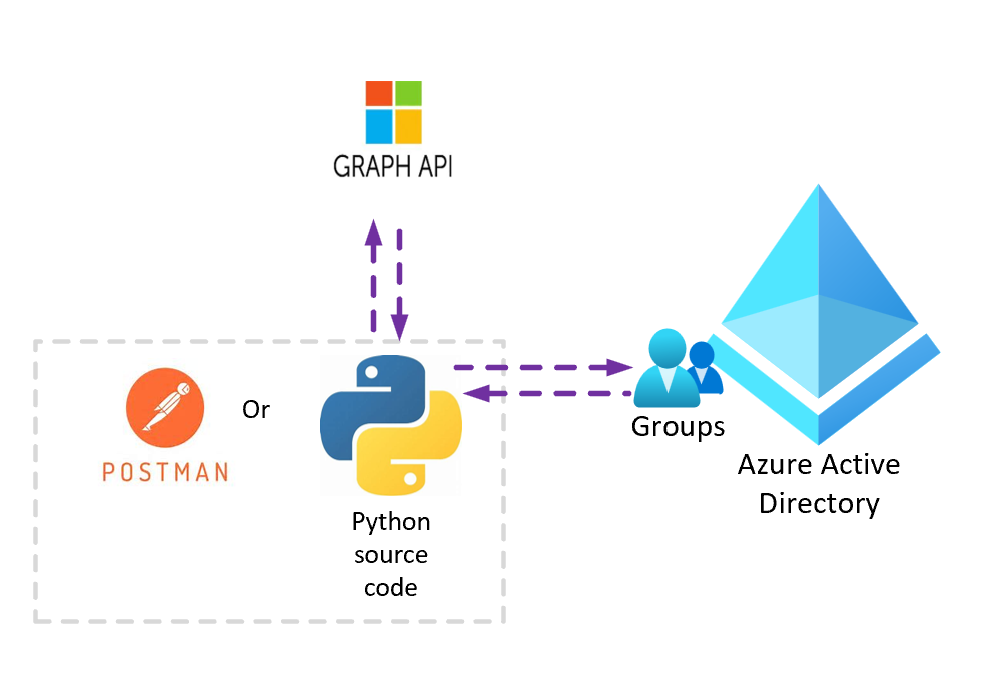
You can refer to below steps for the scenarios in which you have Azure AD service principle with required permissions to create Security Groups in Azure Active Directory and need to call Microsoft Graph REST APIs from your dev or local environment via Postman or through python code.
First step is to register a client application with Azure AD and assign required permissions to create AD groups
1. Sign in the Azure portal, search for and select Azure Active Directory.
2. In the left panel, under Manage, select App registrations > All Applications > Select your registered application (Service Principal Account) > API Permissions
3. Least Privileged Permissions required to create AAD groups are:
- Group.Read.All
- Group.ReadWrite.All
- Group.Create
Python Source Code:
Refer attached python source code (SecurityGroupCreatePythonSample.zip)
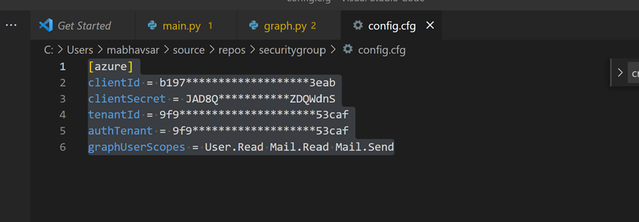
- Update ClientId, ClientSecret and Tenant details in config.cfg file
- Update Request body to create new group in graph.py file
- Install Required dependencies to build the project.
python3 -m pip install azure-identity python3 -m pip install msgraph-core -
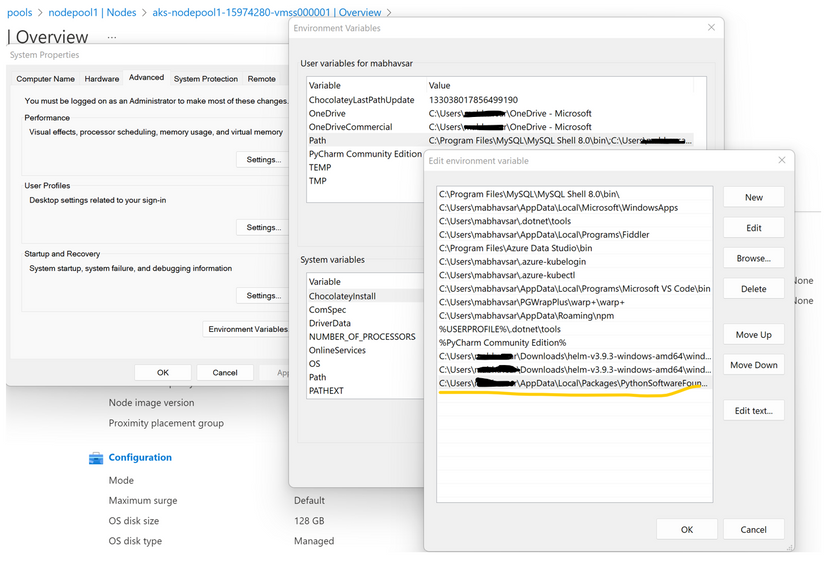
Ensure that installed package script path are added into System Environment Variables.
- Run Main.py file. Choice 6 and 7 are the methods to list or create group using SPN (App Only Authentication)
Reference Link:
Build Python apps with Microsoft Graph - Microsoft Graph | Microsoft Docs
Step 7: Build Python apps with Microsoft Graph - Microsoft Graph | Microsoft Docs
Step 8: Build Python apps with Microsoft Graph - Microsoft Graph | Microsoft Docs
Postman:
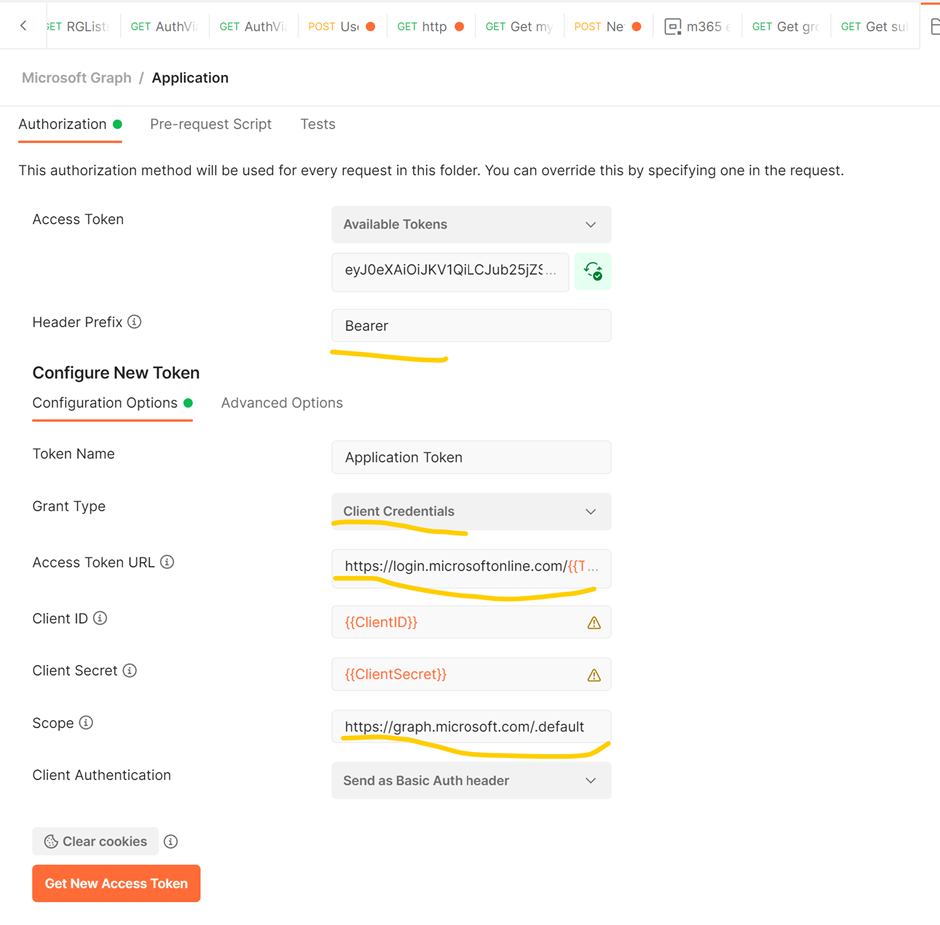
Create Authorization Header in Postman Requests Collection Folder Level:
Access Token Url: https://login.microsoftonline.com/{{TenantID}}/oauth2/v2.0/token
Scope: https://graph.microsoft.com/.default
Grant_Type = Client Credentials
Rest API to create Group:
Url: https://graph.microsoft.com/v1.0/groups
Request Type: Post
Authorization Type: Bearer Token. Copy the access token created from above step
Request Body:
Reference Link:
Use Postman with the Microsoft Graph API - Microsoft Graph | Microsoft Docs
Note:
- If SPN is granted with Delegated permission, you need to follow User Authorization Code to generate access token
- If SPN is granted with Application permission, you can follow Grant type= Client Credentials
Published on:
Learn moreRelated posts
Fix invalid Microsoft service API permissions in SharePoint
Learn how to fix invalid Microsoft service API permissions in SharePoint and ensure smooth SPFx solution deployment.
Microsoft Azure - the platform intelligence runs on
Microsoft Dynamics 365 vs Salesforce: A Practical Comparison for Enterprise Teams
In many organizations currently using Salesforce, the friction does not initially feel like a CRM problem. It feels like extra steps throughou...
Restricting Access is The Most Important Step in a Microsoft 365 Copilot Deployment
I was asked what the most important step is in the deployment of Microsoft 365 Copilot. It's a good question. Put simply, restricted access is...
Microsoft 365 Copilot in Word: Improved support for complex edits
Microsoft 365 Copilot in Word will support complex edits like tracked changes, comments, and document structure while preserving formatting an...
Copilot Notebooks available in Microsoft 365 Copilot Chat for Basic users
Copilot Notebooks will be available in Microsoft 365 Copilot Chat for Basic users starting mid-June 2026, providing a persistent AI-powered wo...
Rolling out a simplified, consistent design and navigation experience in Viva Engage
Viva Engage is updating to a simplified, consistent design and navigation across web and Teams, improving usability and reducing clutter. The ...
Microsoft 365 Copilot: Retirement of Sora video generation experience (Frontier)
The Sora video generation experience in the Frontier program will retire between mid and late June 2026. Users will lose access to create new ...