How to control access to identity-specific folders in Azure Blob Storage using ABAC
An example use case:
I have an Azure Blob Container named "my-org-documents"; a specific folder should be shared across all the identities. However, each identity can only write into their subfolders.
I will use the below identities as example:
[email protected] (AD user)
ExampleMI12 (managed identity)
I have created a path called test, managedidentity and sharedfolder under the container, so the structure is as below:
my-org-documents/test
my-org-documents/managedidentity
my-org-documents/sharedfolder
My task is completed when:
- Active Directory user "test" is able to read/write into sharedfolder
- Active Directory user "test" is able to read/write into test folder but not into managedidentity folder.
- Managed Identity "ExampleMI12" is able to read/write into sharedfolder
- Managed Identity "ExampleMI12" is able to read/write into "ExampleMI12" folder but not into test folder.
Scoping the role assignment:
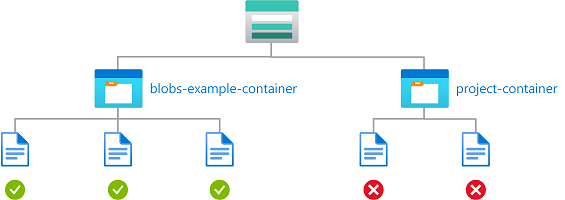
In such scenario, you can achieve the target by assigning "Storage Blob Data Contributor" to the required identity while applying ABAC conditions to add more control over folder access.
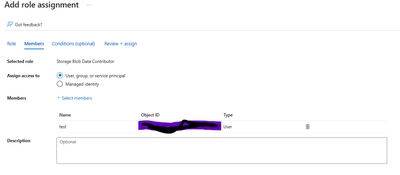
Configuring the user permissions:
- Assigning "Storage Data Contributor role" to user "test" on the storage account level.
-Then, in the conditions tab, I will add the below policy:
The above ABAC policy will only allow read/write access to "test" and "sharedfolder" paths, while it will deny access to all the other folders inside the "my-org-document" container or any other container inside the storage account.
Configuring the managed identity permissions:
- Assigning "Storage Data Contributor role" to managed identity "ExampleMI12" on the storage account level.
- Then, in the conditions tab, I will add the below policy:
Conclusion:
In this scenario, I was able to control folder level access for AD identities by assigning a role to each identity while adding specific ABAC conditions that will add more granularity over the wide role access.
Note: For ADLS endpoint, the ABAC policy should be modified to remove the ending slash from the blob path. Similar to the below example:
Note:
Please add "microsoft.storage/storageAccounts/blobServices/containers/blobs/runAsSuperUser/action" action on all conditions if:
1- The role definition contains this action, such as "Storage blob data owner"
2- The storage accounts included in this condition have hierarchical namespace enabled or might be enabled in the future.
Published on:
Learn moreRelated posts
Setting up Power BI Version Control with Azure Dev Ops
In this blog post is a way set up version control for Power BI semantic models (and reports) using the PBIP (Power BI Project) format, Azure D...
Azure Developer CLI (azd) – March 2026: Run and Debug AI Agents Locally, GitHub Copilot Integration, & Container App Jobs
Run, invoke, and monitor AI agents locally or in Microsoft Foundry with the new azd AI agent extension commands. Plus GitHub Copilot-powered p...
Writing Azure service-related unit tests with Docker using Spring Cloud Azure
This post shows how to write Azure service-related unit tests with Docker using Spring Cloud Azure. The post Writing Azure service-related uni...
Azure SDK Release (March 2026)
Azure SDK releases every month. In this post, you find this month's highlights and release notes. The post Azure SDK Release (March 2026) appe...
Specifying client ID and secret when creating an Azure ACS principal via AppRegNew.aspx will be removed
The option to specify client ID and secret when creating Azure ACS principals will be removed. Users must adopt the system-generated client ID...
Azure Developer CLI (azd): Run and test AI agents locally with azd
New azd ai agent run and invoke commands let you start and test AI agents from your terminal—locally or in the cloud. The post Azure Developer...
Microsoft Purview compliance portal: Endpoint DLP classification support for Azure RMS–protected Office documents
Microsoft Purview Endpoint DLP will soon classify Azure RMS–protected Office documents, enabling consistent DLP policy enforcement on encrypte...
Introducing the Azure Cosmos DB Plugin for Cursor
We’re excited to announce the Cursor plugin for Azure Cosmos DB bringing AI-powered database expertise, best practices guidance, and liv...