Helm charts managed through Terraform to deploy an Azure SecretProviderClass on AKS

Introduction
In this article we will see how to benefit from the advantages of two infrastructure and template management solutions: Helm charts and Terraform.
In order to make the exercise challenging and to prove that the use of these two features works well, I deliberately chose to use the SecretProviderClass because it is a complex Kubernetes resource type to model.
For more details on the SecretProviderClass, please consult the following article that points out how to create a SecretProviderClass using user-assigned identity to access your key vault.
All the code used in this article is available here on GitHub: JamesDLD/terraform-azurerm_kubernetes-helm-chart-SecretProviderClass
Prerequisite
- Access to an existing Azure Kubernetes Service (AKS) cluster.
- You already have configured the Azure Key Vault provider for Secrets Store CSI Driver in an Azure Kubernetes Service (AKS) cluster.
Terraform providers & authentication
The trick here is to retrieve the Kubernetes certificate from the azurerm_kubernetes_cluster resource and pass it to the helm provider.
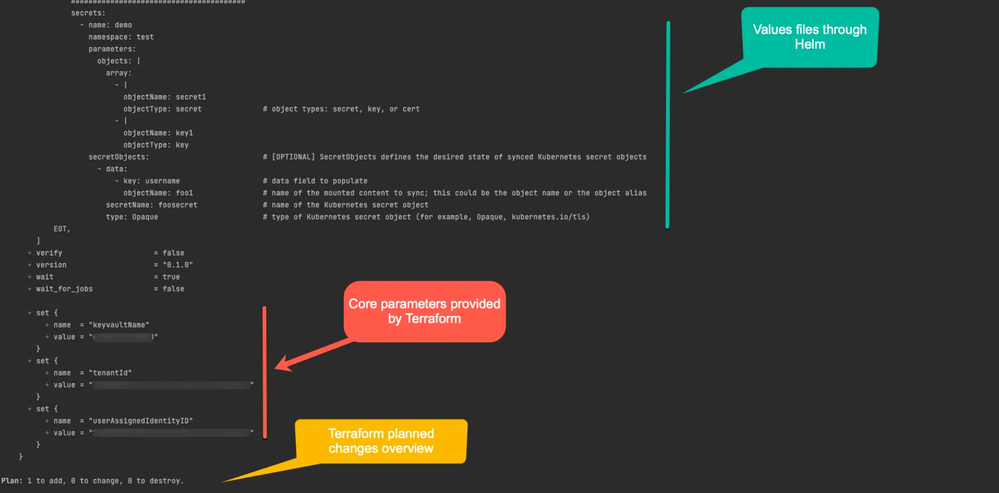
Terraform Helm release
In this section we highlight the following tips:
- Use Helm values files.
- Pass parameters from Terraform to the Helm chart through the “set” function.
- Dynamically retrieve the Azure Tenant ID from Terraform and pass it to the Helm chart.
Helm chart template
The following manifest file manages the Kubernetes SecretProviderClass object and was designed using the following requirements:
- Ability to create multiple SecretProviderClass Kubernetes objects using the range action.
- Use in order of preference the values provided by the current “range” (file “value-demo.yaml”), then the default values (file “value.yaml”) then those provided by Terraform (“set” function).
Terraform plan
What’s interesting here with Terraform is that we can see the planned changes and we can pass Terraform known information like the Azure Tenant ID and core parameters like the target Azure Key Vault.
Conclusion
Using Terraform and Helm charts will help you reap the benefits of both worlds:
- Make full use of your teams’ skills.
- Pass calculated values from your cloud provider without writing them in your code.
- Manage planned changes that new git commits plan to do before applying them in production.
See You in the Cloud
Jamesdld
Published on:
Learn moreRelated posts
Azure DevOps and GitHub: Journeying into the AI Era
AI is changing how software gets planned, built, and reviewed. As teams adopt agentic development, the platform underneath those workflows mat...
Introducing azure-functions-skills: An AI-Era Workspace for Azure Functions (Preview)
azure-functions-skills gives GitHub Copilot CLI, Claude Code, Codex CLI, and VS Code the skills, MCP configuration, hooks, and instructions ne...
Announcing the Public Preview of Integrated Embeddings in Azure Cosmos DB: Build AI Apps With Embeddings That Stay in Sync
AI applications built on Azure Cosmos DB depend on embeddings for grounded results. Keeping them in sync with your data is the hard part: it m...
Introducing OmniVec: An Open-Source Embedding Platform for AI Apps on Azure
Today we are open-sourcing OmniVec, a platform for building and operating the embedding pipelines that keep the vector representation of your ...
Azure Cosmos DB All Versions and Deletes Change Feed Mode is Now Generally Available
Modern applications don’t just write data and move on. They react to it. A new order triggers an inventory update. A profile change sync...
Change Partition Keys in Azure Cosmos DB is Now Generally Available
We’re excited to announce the general availability of Change Partition Key in Azure Cosmos DB for NoSQL, now with online copy support. Y...
Announcing the General Availability of Per Partition Automatic Failover for Azure Cosmos DB NoSQL
Today, we are excited to announce the General Availability of Per Partition Automatic Failover (PPAF) for Azure Cosmos DB NoSQL API. PPAF is a...
Public Preview: AI-powered Azure Cosmos DB Migration Assistant for RDBMS to NoSQL
Today, we are excited to announce the public preview of the Azure Cosmos DB Migration Assistant for RDBMS to NoSQL, now available in the Azure...
Azure Cosmos DB MCP Toolkit Is Now Generally Available — Bringing Your Database to AI Agents at Scale
Since we introduced the Azure Cosmos DB MCP Toolkit at Ignite 2025 in preview, the response has been clear: developers want a straightforward ...
Announcing General availability of the Azure Cosmos DB vNext emulator
The Azure Cosmos DB vNext emulator is generally available today. It ships as a Docker image that runs on Linux, macOS, and Windows, on both x6...
