Migrate to Azure Firewall Premium in Secured vWAN hub with preserved Public IP addresses

A Secured virtual hub uses an associated Firewall (Azure Firewall, third-party security as a service (SecaaS) provider, or both.) and routing policies for governance and protection. This blog looks at the steps to successfully migrate Azure Firewall in your secure virtual hub while preserving the Public IPs already assigned to the Azure Firewall during migration. A schedule down-time should be planned for this migration.
Step 1. Migrate from Classic to Firewall Policy: This is essential if classic rules are used in the current Firewall. Firewall management tool is best suited for Firewall policies, hence ensure that the classic rules are all moved to Firewall policy. Follow this link to migrate classic rules to Firewall policy. (Steps 1 to 3)
Step 2. Back up the Azure Firewall resource
This is a recommended process in case of browser failure or loss of access to terminal during this transition. The migration step briefly involves deallocation of the Firewall and re-allocating the Firewall again while using a placeholder to retain the assigned public IPs. The backup process ensures that you have a copy of your current configuration in the case of a browser hang or internet connectivity issue during the process.
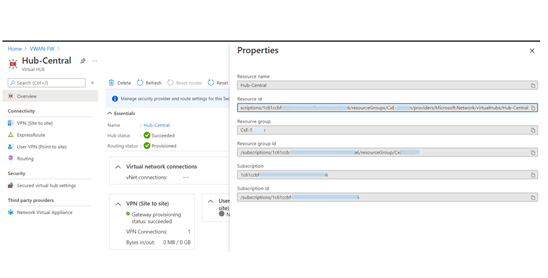
An alternative is to go to the Virtual Hub and copy the Hub ID and save it. This ID retains the definition for the properties of each unique Azure Firewall virtual hub and may be used later.
Go to Resource Group ->VWAN -> Virtual Hub ->(Click on Name) Properties -> Resource ID. Copy and keep this value.
Step 3. Deallocate and Re-allocate Azure Firewall with new Firewall premium tier and reserved Public IPs using the steps below
(Note: Minimum PowerShell Version Supported: PowerShell Gallery | Az 6.5.0)
When the deployment completes, confirm you now have Premium Firewall SKU and the Public IP addresses are available. You can now configure all the additional Azure Firewall Premium features.
For more information about Azure Firewall premium:
Azure Firewall artifacts in Github
Azure Firewall Monitor Workbook with Premium Features view
Published on:
Learn moreRelated posts
How Azure AI Search Improves SharePoint Knowledge Retrieval for Microsoft Copilot
Microsoft Copilot is transforming how businesses interact with enterprise data. From generating summaries and answering queries to assisting c...
Eliminate LLM Cold starts: Load models up to 6x Faster with Azure Blob Storage and Run:AI Model Streamer
Stop paying for idle GPUs while model weights copy to disk. Stream them straight into GPU memory instead with Run:AI Streamer from Azure Blob ...