Generally Available: Windows Server 2012 and 2012 R2 Extended Security Updates enabled by Azure Arc
We are excited to announce that Windows Server 2012 and 2012 R2 Extended Security Updates (ESUs) enabled by Azure Arc is now Generally Available. Windows Server 2012 and 2012 R2 are going End of Support on October 10, 2023. With ESUs, customers who are running Windows Server 2012 on-premises or in other clouds can get three more years of critical security updates from Microsoft to protect their End of Life infrastructure.
Why leverage Windows Server 2012 ESUs enabled by Azure Arc?
Windows Server 2012 ESU’s enabled by Azure Arc afford customers financial, management, and security benefits, beyond traditional Windows Server 2012 ESUs from Volume Licensing:
- Monthly PAYG. Customers have no upfront annual commitments and are able to pay for what they need with the flexibility to deactivate ESU licenses mid-year as they migrate and modernize workloads to Azure.
- Azure billing. As an Azure billed service, customers are able to decrement WS2012 ESUs enabled by Azure Arc from their MACC and can apply Azure Consumption Discounting (ACD) for price savings.
- Seamless delivery. Azure Arc identifies and provides an inventory of all of the customers’ Windows Server 2012 and 2012 R2 servers, and with on-time point and click enrollment eliminates the need for annual MAK key deployment.
- Licensing flexibility. Customers have the ability to mix and match Standard and Datacenter licensing, and virtual core and physical core models, eliminating the need to match SKUs with their underlying host.
- Azure management. Customers benefit from free access to Azure Update Manager, Azure Machine Configuration, and Azure Change Tracking and Inventory (AMA based) for their Azure Arc-enabled servers enrolled in WS2012 ESUs through Arc.
How can you enroll in Windows Server 2012 ESUs enabled by Azure Arc?
Taking advantage of this exciting new offer is as easy three steps: (1) onboard your servers to Azure Arc, (2) provision Windows Server 2012 Arc ESU licenses in Azure, and (3) link ESU licenses to your Azure Arc-enabled servers for access to critical security patches.
First, customers onboard their Windows Server 2012 and 2012 R2 machines to Azure Arc, deploying the Connected Machine agent onto their servers, using automation tool like Configuration Manager, PowerShell, or Group Policy. Customers can select from myriad networking options including public endpoint, proxy connectivity, and private link.
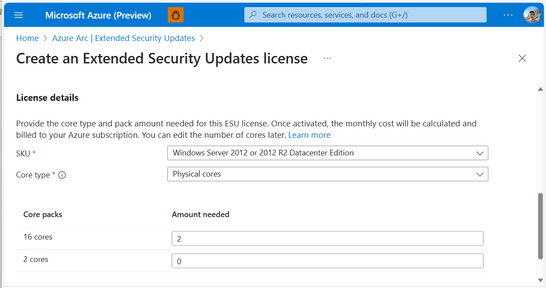
Next, customers provision Windows Server 2012 Extended Security Update licenses, specifying Standard or Datacenter edition and the number of cores (virtual or physical). Customers can modify the number of cores associated with a license and can deactivate/activate licenses. Billing for licenses will commence from End of Support on October 10, 2023. Extended Security Updates cost 100% of the full license price for Windows Server 2012 / 2012 R2. Note, this step requires attesting to meeting the Software Assurance and licensing requirements for using Extended Security Updates.
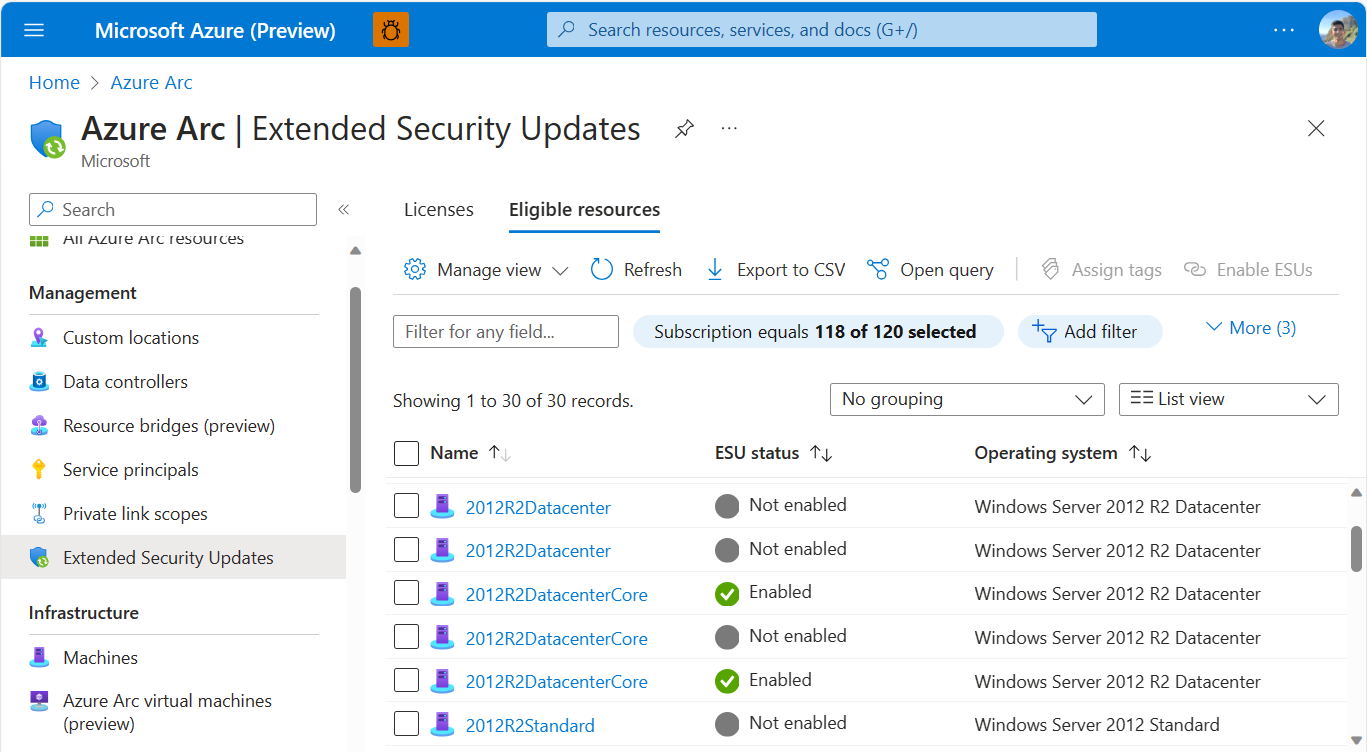
Finally, customers must link their Windows Server 2012 Extended Security Update licenses to their Azure Arc-enabled servers, to enroll the machines in ESUs. Customers do not need to re-enroll each year or manage any MAK Keys. Moreover, customers have the flexibility to use whatever first or third-party patching solution they prefer to receive the actual Windows Server 2012 ESU OS patches. Customers can utilize additional Azure services like Microsoft Defender for Cloud and Microsoft Sentinel to further secure their End of Support infrastructure.
With Windows Server 2012 and 2012 R2 End of Support days away, the time is now to onboard your server estate to Azure Arc and take advantage of this new offer. Extending Azure security, monitoring, and governance from cloud to edge, Azure Arc best positions our End-of-Life infrastructure customers as they migrate to innovate with Azure.
Get started today: Deliver Extended Security Updates for Windows Server 2012. For more information on pricing, see below and https://aka.ms/ArcESUPricing.
Published on:
Learn moreRelated posts
Copilot Code Reviews for Azure Repos
Over the last several years, we have encouraged customers to move their repositories from Azure Repos to GitHub to take advantage of the lates...
Enterprise Live Migrations: Moving from Azure DevOps Repo to GitHub with minimal disruption
Over the last several years, we’ve encouraged customers to move their repositories from Azure Repos to GitHub to take advantage of the latest ...
Enterprise Live Migrations: Moving from Azure DevOps Repo to GitHub with minimal disruption
Over the last several years, we’ve encouraged customers to move their repositories from Azure Repos to GitHub to take advantage of the latest ...
Introducing Azure HorizonDB - PostgreSQL
Run enterprise Postgres workloads on Azure HorizonDB with around 3x the throughput of self-managed deployments — zone-resilient by default, no...
Azure DevOps and GitHub: Journeying into the AI Era
AI is changing how software gets planned, built, and reviewed. As teams adopt agentic development, the platform underneath those workflows mat...