Helm charts managed through Terraform to deploy an Azure SecretProviderClass on AKS

Introduction
In this article we will see how to benefit from the advantages of two infrastructure and template management solutions: Helm charts and Terraform.
In order to make the exercise challenging and to prove that the use of these two features works well, I deliberately chose to use the SecretProviderClass because it is a complex Kubernetes resource type to model.
For more details on the SecretProviderClass, please consult the following article that points out how to create a SecretProviderClass using user-assigned identity to access your key vault.
All the code used in this article is available here on GitHub: JamesDLD/terraform-azurerm_kubernetes-helm-chart-SecretProviderClass
Prerequisite
- Access to an existing Azure Kubernetes Service (AKS) cluster.
- You already have configured the Azure Key Vault provider for Secrets Store CSI Driver in an Azure Kubernetes Service (AKS) cluster.
Terraform providers & authentication
The trick here is to retrieve the Kubernetes certificate from the azurerm_kubernetes_cluster resource and pass it to the helm provider.
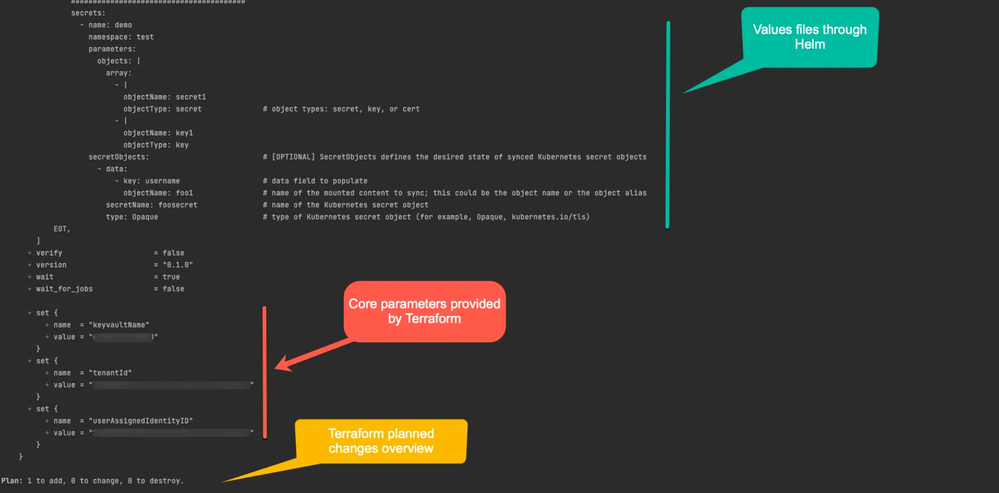
Terraform Helm release
In this section we highlight the following tips:
- Use Helm values files.
- Pass parameters from Terraform to the Helm chart through the “set” function.
- Dynamically retrieve the Azure Tenant ID from Terraform and pass it to the Helm chart.
Helm chart template
The following manifest file manages the Kubernetes SecretProviderClass object and was designed using the following requirements:
- Ability to create multiple SecretProviderClass Kubernetes objects using the range action.
- Use in order of preference the values provided by the current “range” (file “value-demo.yaml”), then the default values (file “value.yaml”) then those provided by Terraform (“set” function).
Terraform plan
What’s interesting here with Terraform is that we can see the planned changes and we can pass Terraform known information like the Azure Tenant ID and core parameters like the target Azure Key Vault.
Conclusion
Using Terraform and Helm charts will help you reap the benefits of both worlds:
- Make full use of your teams’ skills.
- Pass calculated values from your cloud provider without writing them in your code.
- Manage planned changes that new git commits plan to do before applying them in production.
See You in the Cloud
Jamesdld
Published on:
Learn moreRelated posts
Azure Arc | On-prem + Multi-cloud Management
Managing Servers, and Kubernetes across on-prem, and multiple clouds, can quickly become complex, especially when you're juggling multiple too...
Scalable AI with Azure Cosmos DB: Bringing Generative AI to Enterprise Scale with Super Insight by AVASOFT
Azure Cosmos DB enables scalable AI-driven document processing, addressing one of the biggest barriers to operational scale in today’s enterpr...
Announcing the Public Preview of Azure Cosmos DB Shell: Open-Source Power Meets AI-Driven Database Automation
Today, we’re thrilled to announce the public preview of Azure Cosmos DB Shell – a powerful, open-source command-line interface that rev...
Azure Blob Storage for AI
Resiliency by Design: Azure Compute
Introducing langchain-azure-cosmosdb: Build Agentic Apps and RAG with One Database
Build AI Agents and RAG Applications with the New LangChain + LangGraph Connector for Azure Cosmos DB Building AI agents and RAG applications ...
