Microsoft Graph activity logs is now generally available

We’re excited to announce the general availability of Microsoft Graph activity logs! Microsoft Graph activity logs give you visibility into HTTP requests made to the Microsoft Graph service in your tenant. With rapidly growing security threats and an increasing number of attacks, this log data source allows you to perform security analysis, threat hunting, and monitor application activity in your tenant.
Some common use cases include:
- Identifying the activities that a compromised user account conducted in your tenant.
- Building detections and behavioral analysis to identify suspicious or anomalous use of Microsoft Graph APIs, such as an application enumerating all users, or making probing requests with many 403 errors.
- Investigating unexpected or unnecessarily privileged assignments of application permissions.
- Identifying problematic or unexpected behaviors for client applications, such as extreme call volumes that cause throttling for the tenant.
You’re currently able to collect sign-in logs to analyze authentication activity and audit logs to see changes to important resources. With Microsoft Graph activity logs, you can now investigate the complete picture of activity in your tenant – from token request in sign-in logs, to API request activity (reads, writes, and deletes) in Microsoft Graph activity logs, to ultimate resource changes in audit logs.
We’re delighted to see many of you applying the Microsoft Graph activity logs (Preview) to awesome use cases. As we listened to your feedback on cost concerns, particularly for ingestion to Log Analytics, we’ve also enabled Log Transformation and Basic Log capabilities to help you scope your log ingestion to a smaller set if desired.
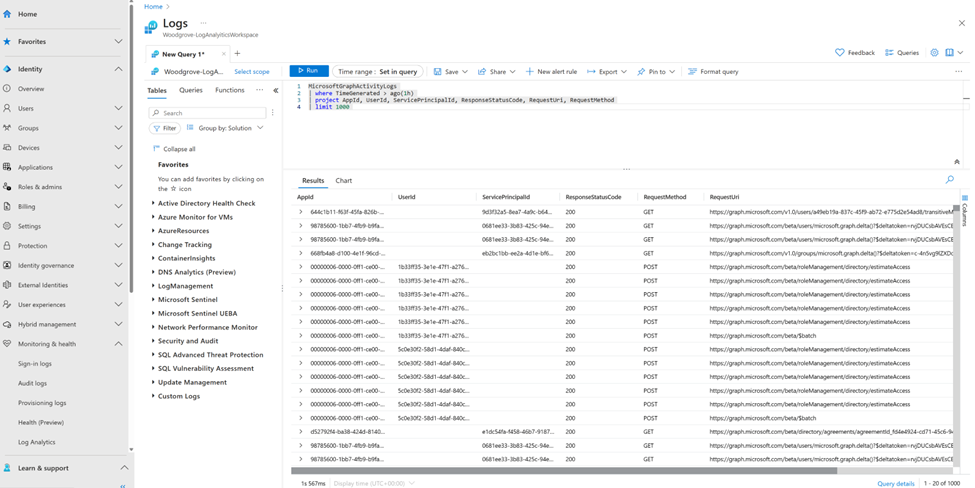
To illustrate working with these logs, we can look at some basic queries:
Summarize applications and principals that have made requests to change or delete groups in the past day:
|
MicrosoftGraphActivityLogs | where TimeGenerated > ago(1d) | where RequestUri contains '/group' | where RequestMethod != "GET" | summarize UriCount=dcount(RequestUri) by AppId, UserId, ServicePrincipalId, ResponseStatusCode |
See recent requests that failed due to authorization:
|
MicrosoftGraphActivityLogs | where TimeGenerated > ago(1h) | where ResponseStatusCode == 401 or ResponseStatusCode == 403 | project AppId, UserId, ServicePrincipalId, ResponseStatusCode, RequestUri, RequestMethod | limit 1000 |
Identify resources queried or modified by potentially risky users:
Note: This query leverages Risky User data from Entra ID Protection.
|
MicrosoftGraphActivityLogs | where TimeGenerated > ago(30d) | join AADRiskyUsers on $left.UserId == $right.Id | extend resourcePath = replace_string(replace_string(replace_regex(tostring(parse_url(RequestUri).Path), @'(\/)+','/'),'v1.0/',''),'beta/','') | summarize RequestCount=dcount(RequestId) by UserId, RiskState, resourcePath, RequestMethod, ResponseStatusCode |
Microsoft Graph activity logs are available through the Azure Monitor Logs integration of Microsoft Entra. Administrators of Microsoft Entra ID P1 or P2 tenants can configure the collection and storage destinations of Microsoft Graph activity logs through the diagnostic setting in the Entra portal. These settings allow you to configure the collection of the logs to a storage destination of your choice. The logs can be stored and queried in an Azure Log Analytics Workspace, archived in Azure Storage Accounts, or exported to other security information and event management (SIEM) tools through Azure Event Hubs. For logs collected in a Log Analytics Workspace, you can use the full set of Azure Monitor Logs features, such as a portal query experience, alerting, saved queries, and workbooks.
Find out how to enable Microsoft Graph activity logs, sample queries, and more in our documentation.
Kristopher Bash
Product Manager, Microsoft Graph
LinkedIn
Learn more about Microsoft Entra:
- See recent Microsoft Entra blogs
- Dive into Microsoft Entra technical documentation
- Learn more at Azure Active Directory (Azure AD) rename to Microsoft Entra ID
- Join the conversation on the Microsoft Entra discussion space
- Learn more about Microsoft Security
Published on:
Learn moreRelated posts
Microsoft 365 Copilot in Word: Improved support for complex edits
Microsoft 365 Copilot in Word will support complex edits like tracked changes, comments, and document structure while preserving formatting an...
Copilot Notebooks available in Microsoft 365 Copilot Chat for Basic users
Copilot Notebooks will be available in Microsoft 365 Copilot Chat for Basic users starting mid-June 2026, providing a persistent AI-powered wo...
Rolling out a simplified, consistent design and navigation experience in Viva Engage
Viva Engage is updating to a simplified, consistent design and navigation across web and Teams, improving usability and reducing clutter. The ...
Microsoft 365 Copilot: Retirement of Sora video generation experience (Frontier)
The Sora video generation experience in the Frontier program will retire between mid and late June 2026. Users will lose access to create new ...
Microsoft 365 & Power Platform Call (Microsoft Speakers) – June 9th, 2026 – Screenshot Summary
Call Highlights SharePoint Quicklinks: Primary PnP Website: https://aka.ms/m365pnp Documentation & Guidance SharePoint Dev Videos Issues...
Microsoft Teams: Improved app and agent access request flows for admin‑blocked apps
Microsoft Teams will introduce a clearer, guided request flow for access to admin-blocked apps and agents, improving user notifications and ad...
Microsoft 365 Archive: File-level archiving General Availability
Microsoft 365 Archive now supports file-level archiving for SharePoint files, enabling cold storage with discoverability. Rolling out worldwid...
Converting Get-MailboxFolderStatistics ids for use with the Graph API
In this article, we discuss how to convert Exchange folderIds (as returned by the Get-MailboxFolderStatistics cmdlet) to the RestId identifier...