Microsoft Graph Activity Log is Now Available in Public Preview

Hi friends,
Today we’re excited to announce the public preview of Microsoft Graph Activity Logs. Have you wondered what applications are doing with the access you've granted them? Have you discovered a compromised user and hoped to find out what operations they have performed? If so, you can now gain full visibility into all HTTP requests accessing your tenant’s resources through the Microsoft Graph API.
*Note: We're enabling the feature starting today. Public preview will be available in all regions within two weeks.
You’re currently able to collect SignIn logs to analyze authentication activity and Audit logs to see changes to important resources. With Microsoft Graph Activity Logs, you can now investigate the complete picture of activity in your tenant – from token request in SignIn logs, to API request activity (reads, writes, and deletes) in Microsoft Graph Activity Logs, to ultimate resource changes in Audit logs.
The Microsoft Graph Activity Logs include information about the request and client application. Some common use cases include:
- Identifying the activities that a compromised user account conducted in your tenant.
- Building detections and behavioral analysis to identify suspicious or anomalous use of Microsoft Graph APIs – such as an application enumerating all users; or making probing requests with many 403 errors.
- Investigating unexpected or unnecessarily privileged assignments of application permissions.
- Identifying problematic or unexpected behaviors for client applications – such as extreme call volumes that exhaust rate-limits for the tenant.
To illustrate working with these logs, we can look at some basic LogAnalytics queries:
Summarize applications and principals that have made requests to change or delete groups in the past day:
|
MicrosoftGraphActivityLogs | where TimeGenerated > ago(1d) | where RequestUri contains '/group' | where RequestMethod != "GET" | summarize UriCount=dcount(RequestUri) by AppId, UserId, ServicePrincipalId, ResponseStatusCode |
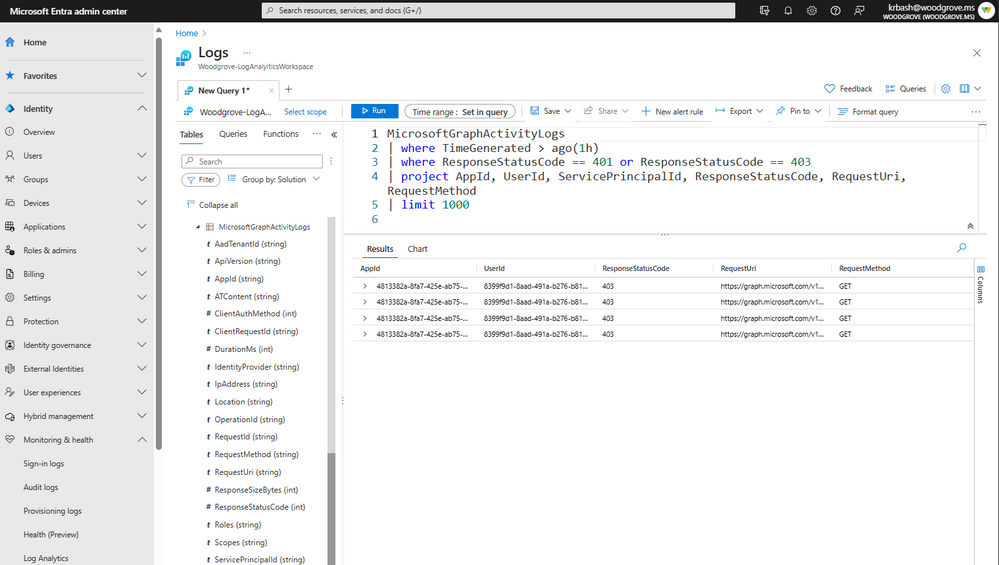
To see recent requests that failed due to authorization:
|
MicrosoftGraphActivityLogs | where TimeGenerated > ago(1h) | where ResponseStatusCode == 401 or ResponseStatusCode == 403 | project AppId, UserId, ServicePrincipalId, ResponseStatusCode, RequestUri, RequestMethod | limit 1000 |
Get top 20 app instances by request count:
|
MicrosoftGraphActivityLogs | where TimeGenerated > ago(1d) | summarize RequestCount=count() by AppId, IpAddress, UserAgent | sort by RequestCount | limit 20 |
Microsoft Graph Activity Logs are available through the Azure Monitor Logs integration of Entra. Administrators can configure the collection and storage destinations of Microsoft Graph Activity Logs through Diagnostic Setting in the Entra Portal. These settings allow you to configure the collection of the logs to a storage destination of your choice. The logs can be stored and queried in an Azure Log Analytics Workspace, archived in Azure Storage Accounts, or exported to other SIEM tools through Azure Event Hubs.
For logs collected to a Log Analytics Workspace, you can use the full set of Azure Monitor Logs features, such as a portal query experience, alerting, saved queries, and workbooks.
Find out about how to enable Microsoft Graph Activity Logs, sample queries, estimated costs, and more in our documentation.
Learn more about Microsoft Entra:
- See recent Microsoft Entra blogs
- Dive into Microsoft Entra technical documentation
- Join the conversation on the Microsoft Entra discussion space and Twitter
- Learn more about Microsoft Security
Published on:
Learn moreRelated posts
Microsoft 365 Copilot for Service – Create case records from customer emails with one click
We are announcing the ability to create case records from customer emails within Outlook in Microsoft 365 Copilot for Service. This feature wi...
SharePoint Framework (SPFx) roadmap update – December 2025
SPFx is powering the future of Microsoft 365. From AI-driven portals to seamless integrations across SharePoint, Teams and Viva, SPFx is drivi...
Exam AB-900: Microsoft 365 Copilot and Agent Administration Fundamentals
Following on the steps of the other AB exams I’ve been writing about my experience with (see Exam AB-730: AI Business Professional &...
Microsoft Copilot (Microsoft 365): Chat History Landing page: Filtering UI Refresh
To help you quickly find the conversations that matter, we’re updating the Chat History filtering experience. This refresh makes the interface...
Microsoft Copilot (Microsoft 365): Capture voice notes in the Microsoft 365 Copilot mobile app
With a Microsoft 365 Copilot license, transform offline discussions into structured, actionable, and searchable content with voice notes in Co...
Microsoft Graph PowerShell SDK V2.34 Makes WAM the Default
The Web Account Manager (WAM) authentication broker becomes the default method for handling interactive Microsoft Graph PowerShell SDK connect...
Microsoft 365: New functionality and prices in 2026
A range of security and AI enhancements have been announced for the Microsoft 365 suite of products in 2026, along with some small price incre...
Automating Microsoft 365 with PowerShell Update 19
Update #19 of the Automating Microsoft 365 with PowerShell eBook is now available. Subscribers can download the updated PDF and EPUB files fro...
Teams admin center: Auto‑updates for Teams Android device firmware and apps will be paused during year‑end holidays
Auto-updates for Teams Android device firmware and apps via Teams admin center will pause from December 20, 2025, to January 12, 2026, to ensu...
OpenAI’s GPT-Image-1.5 model is now available in Microsoft 365 Copilot
Microsoft 365 Copilot will replace GPT-4o with OpenAI’s GPT-Image-1.5 from mid-December 2025 to late January 2026, enhancing image generation ...