Maximizing Effectiveness: Best Practices for Azure DDoS Protection and Application Resilience

Azure DDoS Protection is constantly innovating to protect customers from ever-changing DDoS attacks. As attacks become more sophisticated, it is important to keep your applications up to date with industry best practices to ensure maximum effectiveness when using Azure DDoS Protection. Below are architectural and design decisions you can make to ensure your resources are resilient to DDoS attacks.
Minimizing Vulnerabilities and Enabling Relevant Protections
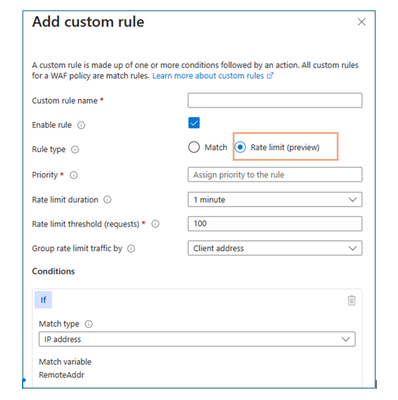
It is important to launch the relevant protection services for your application. If you have any applications deployed to the internet, enabling DDoS Protection is vital. Any application that is open to the internet is vulnerable to Layer 3 and Layer 4 attacks. If your application is deployed to the web, enabling Web Application Firewall will protect you from Layer 7, application attacks. A WAF solution can react to security threats faster by centrally patching vulnerabilities instead of securing each individual web application. WAF can be attached to Azure’s Application Gateway and Azure Front Door. WAF now offers rate-limiting, meaning customers can create rules that restrict source IP addresses to a maximum limit of requests per minute. Both work in tandem to ensure protection on all fronts.
While these services will protect you if deployed during an attack, it is beneficial to deploy them during peace times to get to know what normal traffic looks like. Knowing these normal patterns will allow you to set up relevant metrics and alerts and help us tailor the experience to your application. As part of Azure DDoS Protection each customer has unique auto-tuned DDoS mitigation policies. Customers can view their policies and filter by IP or traffic type in the Azure Portal metrics, see more here.
It is useful to set up metrics and notifications for your applications. You can use the logs in Azure portal to view traffic patterns during an attack. You can see how much traffic is being dropped and why, along with many other useful insights, see more here.
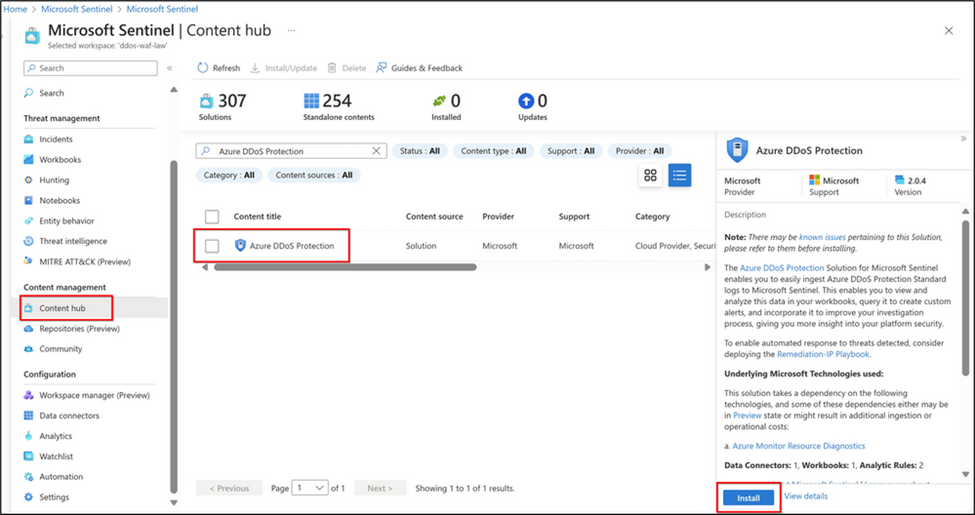
Azure DDoS can be integrated with Microsoft Sentinel to ingest DDoS protection logs for analysis and monitoring. From Sentinel, custom alerts can be created and organized for analysis. Sentinel can also be used with Azure Firewall to automate responses to DDoS attacks. For more information on Microsoft Sentinel integrations, see more here.
While in peacetime, it is a good idea to simulate a DDoS attack to see how your systems react. You can use one of our attack simulation partners, see more info here.
While our protection services handle attacks, there are things you can do to make sure your applications see minimal impact while we are mitigating attacks. These practices also strength your application’s overall security.
Design for Security and Defense In-Depth
It is essential to consider security at every level of development. To make sure your applications are secure it is important to layer defensive strategies.
Minimizing your surface area helps lower the risk of attacks. One way this can be done is by using approval lists to close any unnecessary IPs or listening ports. With fewer entry points, attacks are less likely to be successful and it is easier to monitor what you have. Customers can utilize Azure Firewall and Bastion to access Azure resources. Firewall adds filtering and real time alerts to applications. Customers can filter out new and emerging bad domains and IPs to keep applications safe from the most recent threats. Azure Firewall Premium also has IDPS, which provides information on bad sources based on intel from the Microsoft Threat Intelligence Center. Bastion enables customers to securely connect to virtual machines from Azure Portal or a native client. When you connect via Azure Bastion, your virtual machines don't need a public IP address, agent, or special client software.
Network security groups can also be used to simplify configuring network security and creating security rules.
It is recommended to deploy virtual networks when possible. While Azure Virtual Networks default to using public IPs as their source IPs, using service endpoints switches service traffic to virtual network private address as the source IP address when accessing Azure from a virtual network.
Lastly, many customers maintain on-prem resources for various reasons, however keeping well known public entities in Azure allows the Azure platform and services to provide added protection. Customers can leverage Azure’s global scale DDoS Mitigation. Azure mitigated what is believed to be the largest DDoS network attack at 3.47 Tbps. Azure has a DDoS capacity to mitigate around 50 Tbps of attack traffic, allowing us to handle attacks without customers seeing an impact much better than most on-prem resources can. If you need to have on-prem resources, it is a good idea to keep them private.
Building for Scalability
Scalability is an application's ability to grow or shrink appropriately to usage. If you see an influx of legitimate traffic, you want your application to be able to handle all those users. However, once this influx is over, you do not want to be paying for unnecessary resources.
Many Azure services and products have auto-scaling features which should be enabled to dynamically allocate resources. Azure DDoS Network Protection also offers cost protection for resources added during an attack.
Instance stickiness, or session affinity is when a client’s requests are always routed to the same servers. This can overwhelm the servers. It is important to make sure any instance can handle any request. Avoid storing session states in memory or using machine specific keys for encryption. To learn more about stickiness see here.
To ensure effective scalability, it is vital to identify and avoid bottlenecks. No amount of scaling out will be able to compensate for a bottlenecked backend.
Scaling in is an equally important part of scalability. Build your applications with resilient retry logic against transient network failures or connection resets. While Azure DDoS Protection and Azure WAF can provide mitigation from attack traffic, your application needs retry logic that can withstand. One way to test if your application has sufficient retry logic, is by launching a simulated DDoS attack. This will let you see how your application acts under the stresses of a DDoS attack. Doing various simulated attacks helps ensure your design is working with Azure Security services to mitigate impact. See this blog post for more on resilient retry logic.
As DDoS attacks become more frequent and easier for malicious actors to utilize, it is prudent to keep up to date with comprehensive protections for your applications. By following the tips above, you can have confidence that your applications are protected on all levels.
Resources:
2022 in Review: DDoS Attack Trends and Insights
Azure DDoS Protection Documentation
Microsoft Digital Defense Report 2022
Azure Web Application Firewall Documentation
New Azure DDoS Solution for Microsoft Sentinel Blog
Using the Retry Pattern to Make Your Cloud Applications More Resilient
Published on:
Learn moreRelated posts
Introducing the Azure Cosmos DB Plugin for Cursor
We’re excited to announce the Cursor plugin for Azure Cosmos DB bringing AI-powered database expertise, best practices guidance, and liv...
Azure DevOps Remote MCP Server (public preview)
When we released the local Azure DevOps MCP Server, it gave customers a way to connect Azure DevOps data with tools like Visual Studio and Vis...
Azure Cosmos DB at FOSSASIA Summit 2026: Sessions, Conversations, and Community
The FOSSASIA Summit 2026 was an incredible gathering of developers, open-source contributors, startups, and technology enthusiasts from across...
Dataverse: Avoid Concurrency issues by using Azure Service Bus Queue and Azure Functions
Another blog post to handle the concurrency issue. Previously, I shared how to do concurrency via a plugin in this blog post and also how to f...
March Patches for Azure DevOps Server
We are releasing patches for our self‑hosted product, Azure DevOps Server. We strongly recommend that all customers stay on the latest, most s...
Azure Developer CLI (azd): Debug hosted AI agents from your terminal
New azd ai agent show and monitor commands help you diagnose hosted AI agent failures directly from the CLI. The post Azure Developer CLI (azd...
A Look Ahead at Azure Cosmos DB Conf 2026: From AI Agents to Global Scale
Join us for Azure Cosmos DB Conf 2026, a free global, virtual developer event focused on building modern applications with Azure Cosmos DB. Da...
Announcing general availability of Azure Confidential Computing (ACC) virtual machines for U.S. government environments
Government agencies have an increased need for secure, verifiable, and compliant cloud environments that adhere to data sovereignty regulation...