Validating FTP traffic scenarios with Azure Firewall

Written by Gopikrishna Kannan (Head of Products: Azure Firewall and Firewall Manager)
Introduction:
The Azure Firewall is a cloud-native and intelligent network firewall security service that can be integrated into many different use cases. It’s a fully stateful firewall as a service with built-in high availability and unrestricted cloud scalability that provides both east-west and north-south traffic inspection.
This blog will discuss FTP scenario with Azure Firewall. FTP or File Transfer Protocol is the most common use case for enterprise customers. FTP may be configured to run in active or passive mode, which determines how the data connection is established.
Azure Firewall supports both Active and Passive FTP scenarios. Passive FTP mode requires FTP client to initiate connection to the server on a specified port range. Passive FTP is the recommended approach for E-W scenarios. In Active FTP mode, the server initiates connection to the client. This approach is typically deployed to support internet clients connecting to the FTP server running behind Azure Firewall and requires more than 250 DNAT ports (Azure Firewall DNAT rule limits) to be opened hitting load balancer limits. By default, Passive FTP is enabled, and Active FTP support is disabled to protect against FTP bounce attacks using the FTP PORT command.
Configuring Passive FTP mode for E-W traffic:
In this setup, I created the environment below with two directly peered VNETs. Client is hosted on 10.5.0.0/24 subnet and server is in 10.1.1.0/24. Both client and server is running Windows Server 2019 and configured to route traffic to the Azure Firewall. Azure Firewall is configured to allow traffic to the FTP server 10.1.1.6 on port 50000-52000, port 20 & 21.
Server 10.1.1.6 is running FileZilla FTP and configured to allow passive FTP on port 50000-52000. I created a temporary user with permission to read/write to the FTP server on a specific directory.
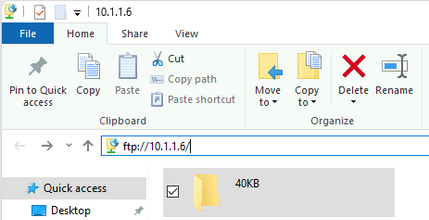
Running the test: On the client, I launched file explorer and ran the command to connect to FTP server 10.1.1.6.
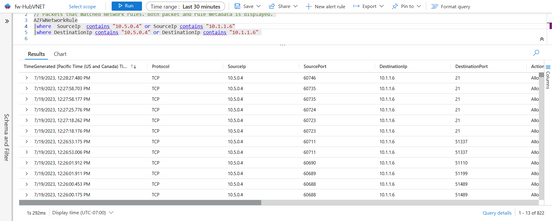
I validated the scenario by copying all the files in the directory and checking the Firewall logs.
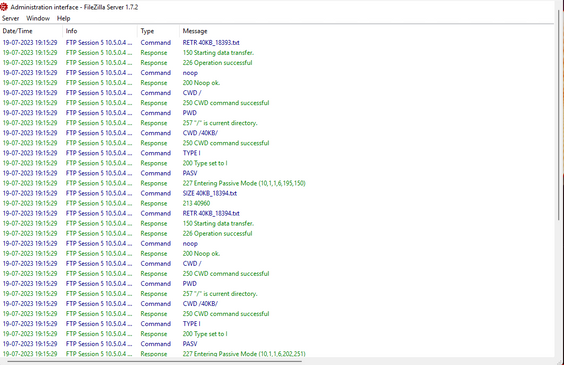
You can also review FTP transactions on the FileZilla Server administration interface.
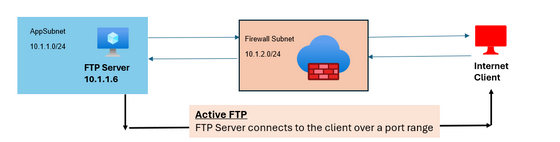
Validating Active FTP mode for internet traffic:
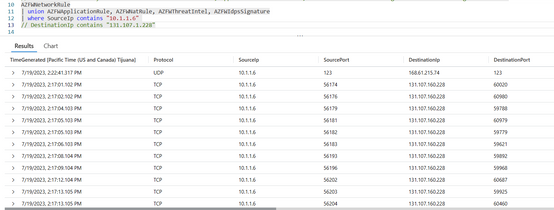
In this scenario, the client is connecting from the internet to the FTP server 10.1.1.6 running behind Azure Firewall. The Firewall is configured to allow DNAT Firewall Public IP on port 21 to FTP server 10.1.1.6. Server 10.1.1.6 has complete access to outbound internet traffic.
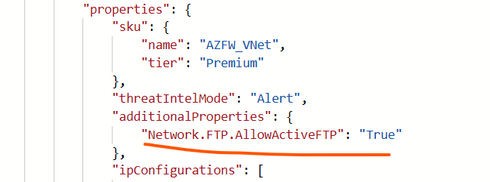
You should enable Active FTP support on Azure Firewall. The simplest way to do this is to export the Firewall template and redeploy with the additional properties updated to allow Active FTP.
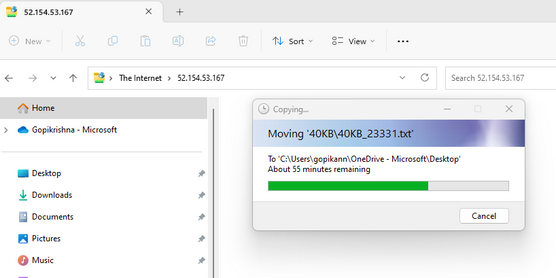
On the internet client, disable Passive FTP (links to instructions are provided below) before launching explorer to start FTP session to the Azure Firewall Public IP. Provide the user credentials and start file transfer by copying the remote folders to your desktop.
Additionally, you can verify the Firewall logs and the FileZilla server to debug transactions errors.
Conclusion:
This covers validating FTP scenario using Azure Firewall. We want to hear from you. Please share your experience and any feedback. Follow the links below to learn more about FTP and help with setup.
File Transfer Protocol - Wikipedia
Azure Firewall FTP support | Microsoft Learn
FileZilla - The free FTP solution (filezilla-project.org)
(537) Filezilla FTP Server Setup for Windows - YouTube
Passive FTP Mode: Enabling / disabling in Internet Explorer (dynabook.com)
Published on:
Learn moreRelated posts
How Azure AI Search Improves SharePoint Knowledge Retrieval for Microsoft Copilot
Microsoft Copilot is transforming how businesses interact with enterprise data. From generating summaries and answering queries to assisting c...
Eliminate LLM Cold starts: Load models up to 6x Faster with Azure Blob Storage and Run:AI Model Streamer
Stop paying for idle GPUs while model weights copy to disk. Stream them straight into GPU memory instead with Run:AI Streamer from Azure Blob ...