Simplify certificate management of on-prem IIS server with Azure Arc & Azure Key Vault VM extension

One common question which I’ve come across is certificate management for web servers. Usually when servers are hosted on Azure there are ways like storing certificates and secrets in Azure Key vault is a viable solution. I’ve come across customers who’re running servers in hybrid and few servers would still remain on-premises because of dependencies. For these web servers managing certificates is a costly affair. Common practice which I’ve seen is admin sharing the certificate with application team on some file share. This has few disadvantages.
- Storing the certificate in file share or on email.
- Based on the number of application team a lot of team gets access to certificates.
- Manually applying updated certificates once the expiry is near also finding which all servers this certificate is being used is a pain if you’ve a big environment with lots of web service.
One better way to handle this scenario is to Store certificate in Azure Key vault centrally and Arc Enable the web server. One last step which will do the magic is Azure Key vault VM Extension. Which can be enabled on Arc Server as extension.
This setup provides the advantages below.
- All the certificates are stored centrally in Azure Key Vault which is protected.
- No application team has got manual access to certificates, on-prem server will pull the certificate based on the managed identity assigned via Azure Arc.
- Once the cert expiry is near Admin/app team need to just goto Azure Key Vault and update the certificate with the latest version. Azure Key vault VM Extension will pull the latest certificate and apply the same to the website.
For auto renewal of certificate, we’ll need to enable IIS Rebind.
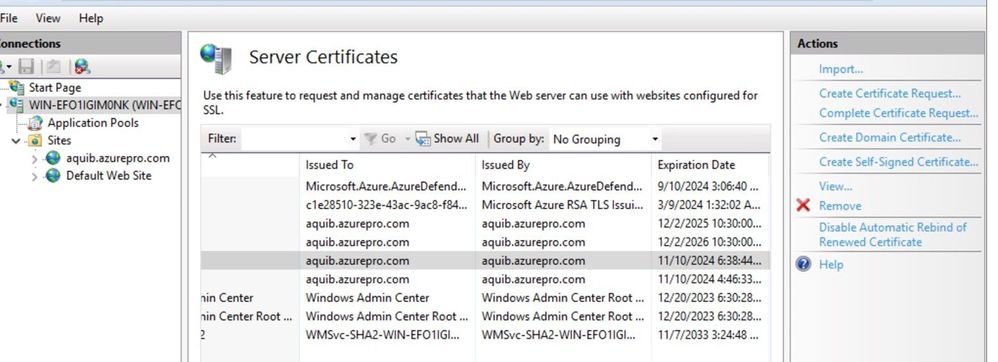
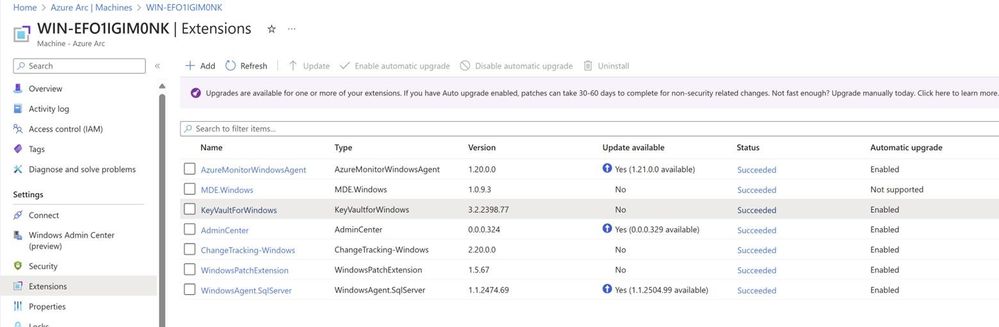
This is how Arc VM Extension looks like when it’s enabled.
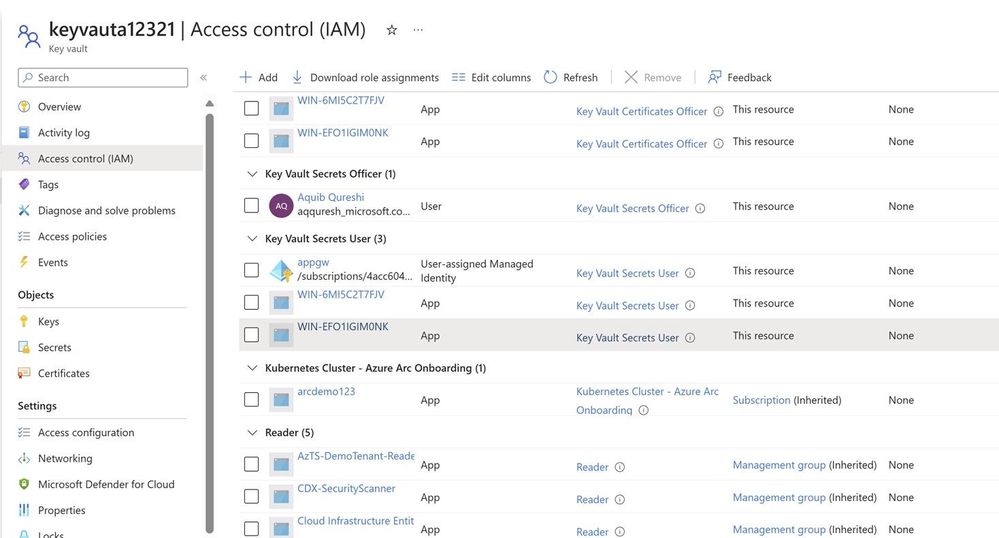
Assigning permission to Arc server to fetch the certificate from keyvault.
You can use access policy on Keyvault as well, it’s supported.
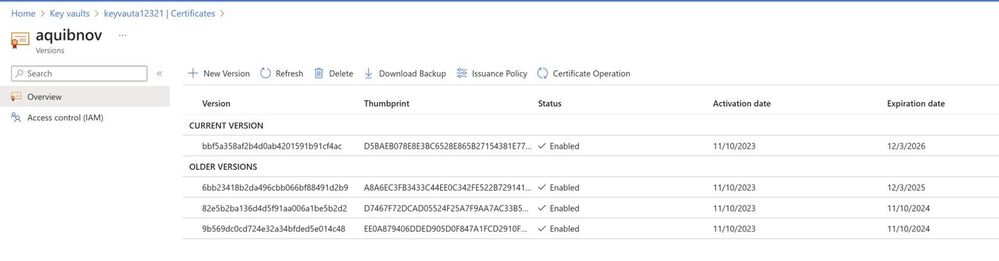
Versions of the certificate/new certificate can be uploaded from key vault certificate blade and looks like below.
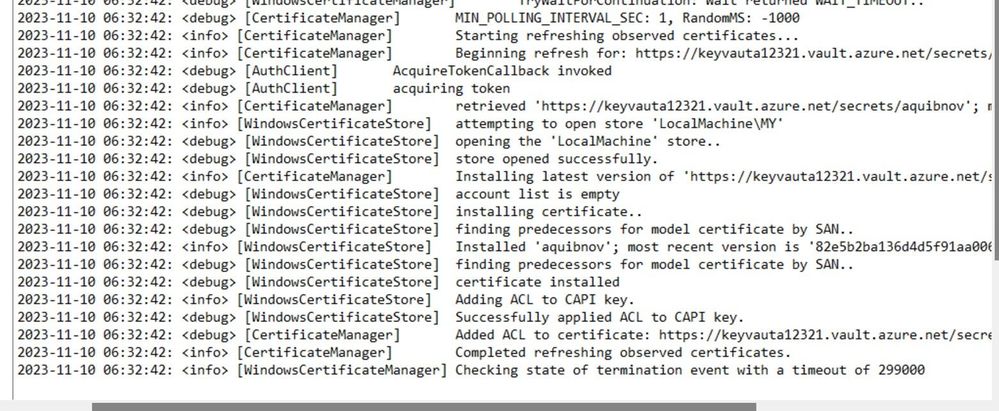
If you’re renewing certificates and wanted to see if certificates are getting pulled down properly or not you can check error logs located here.
C:\ProgramData\Guestconfig\extension_logs\Microsoft.Azure.Keyvault.keyvaultforwindows
If you’re running Azure VM similar thing can be achieved :
https://learn.microsoft.com/en-us/azure/virtual-machines/extensions/key-vault-windows
Cert Rebind in IIS:
https://learn.microsoft.com/en-us/iis/get-started/whats-new-in-iis-85/certificate-rebind-in-iis85
Published on:
Learn moreRelated posts
Introducing Azure HorizonDB - PostgreSQL
Run enterprise Postgres workloads on Azure HorizonDB with around 3x the throughput of self-managed deployments — zone-resilient by default, no...
Azure DevOps and GitHub: Journeying into the AI Era
AI is changing how software gets planned, built, and reviewed. As teams adopt agentic development, the platform underneath those workflows mat...
Introducing azure-functions-skills: An AI-Era Workspace for Azure Functions (Preview)
azure-functions-skills gives GitHub Copilot CLI, Claude Code, Codex CLI, and VS Code the skills, MCP configuration, hooks, and instructions ne...
Announcing the Public Preview of Integrated Embeddings in Azure Cosmos DB: Build AI Apps With Embeddings That Stay in Sync
AI applications built on Azure Cosmos DB depend on embeddings for grounded results. Keeping them in sync with your data is the hard part: it m...
Introducing OmniVec: An Open-Source Embedding Platform for AI Apps on Azure
Today we are open-sourcing OmniVec, a platform for building and operating the embedding pipelines that keep the vector representation of your ...