Apply CIS compliant Azure Security baselines through Azure Automanage!
We are thrilled to announce that Azure Automanage Machine Best Practices now enables you to apply CIS aligned Azure security baselines through Automanage Machine Configuration.
Azure Automanage Machine Best Practices is a consolidated management solution that simplifies daily server management through effortless automation by handling the initial setup and configuration of Azure best practice services. Automanage continuously monitors machines across their entire lifecycle, automatically bringing them back into conformance should they drift from the desired state. And the best part - Automanage machine best practices is generally available and free to use! You only pay for the services you enable, just as you would if you were doing it all manually, without any additional cost.
Azure has released a new Windows server security benchmark that is fully compliant with the newly released CIS Azure Compute Microsoft Windows Server 2019 Benchmark. Working in partnership with CIS, this new compute benchmark includes cloud-specific security controls and removes non-applicable controls that have no significant risk impact in cloud environment.
What’s new for Azure Automanage machine best practices and server security baselines
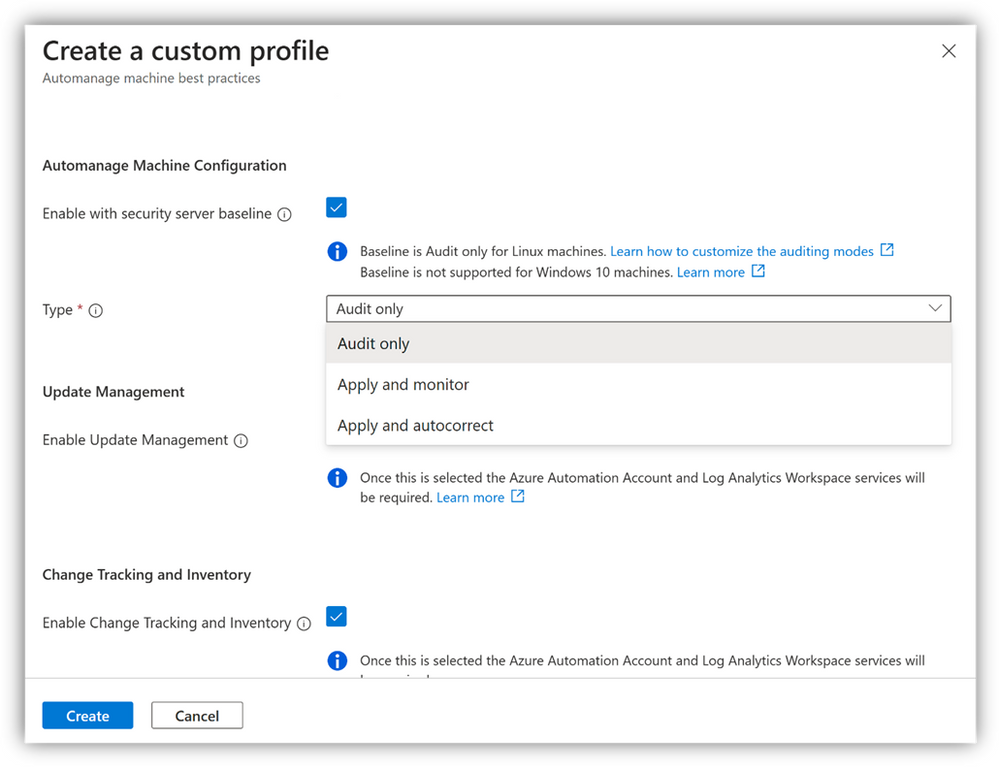
Using Automanage Machine Best Practices, you can now apply the CIS compliant Windows baselines by leveraging the Automanage Machine Configuration offering. Machine Configuration is a key service that you can enable on your Azure Virtual Machines and Arc-enabled servers through an Automanage configuration profile. Just as Machine Best Practices lets customers describe desired state for management services, Machine Configuration provides the same functionality within the actual resources, by auditing or configuring operating system settings as code. When you select Machine Configuration in your configuration profile, Machine Configuration will automatically apply Azure Windows security baseline settings*.
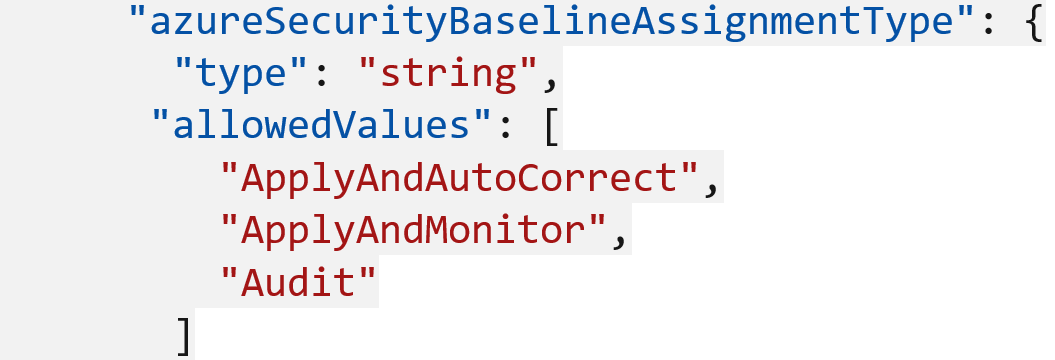
Machine Configuration can deliver changes within a machine in three different ways. This can be done by assigning the following modes as a parameter of machine configuration definitions that support the policy effect DeployIfNotExists (DINE) -
- Audit - This mode reports the current state of the machine but does not implement any change.
- Apply and monitor - This mode applies the recommended change to the machine once and then monitors it for deflections. If the configuration becomes non-compliant at any time, a manual remediation needs to be triggered to make any change.
- Apply and autocorrect - This mode applies the changes to the machine. If there is a deflection, the local service within the machine corrects it at the next evaluation.
These modes can be assigned through the Automanage Portal experience here (details in the Get started section below) or through an ARM template.
Get started
Let’s dive deeper and show you how to get started:
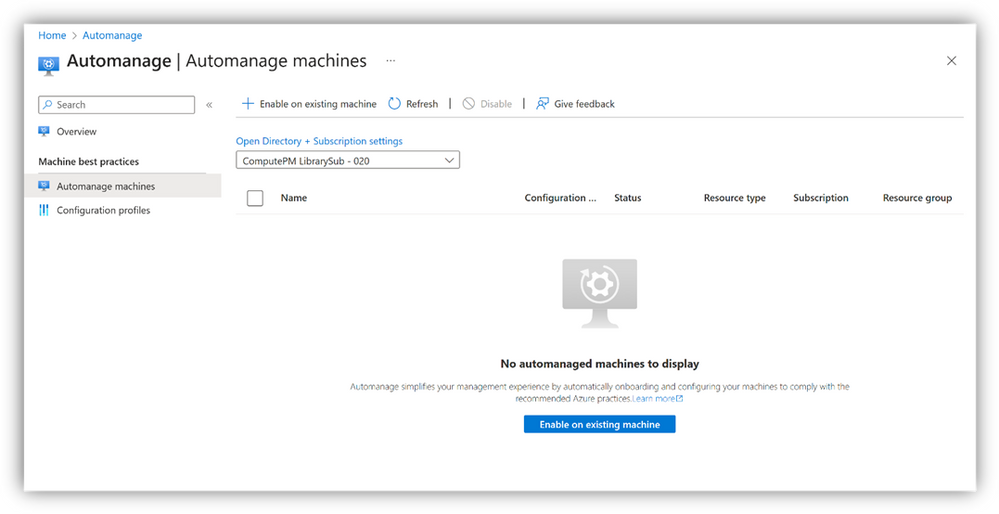
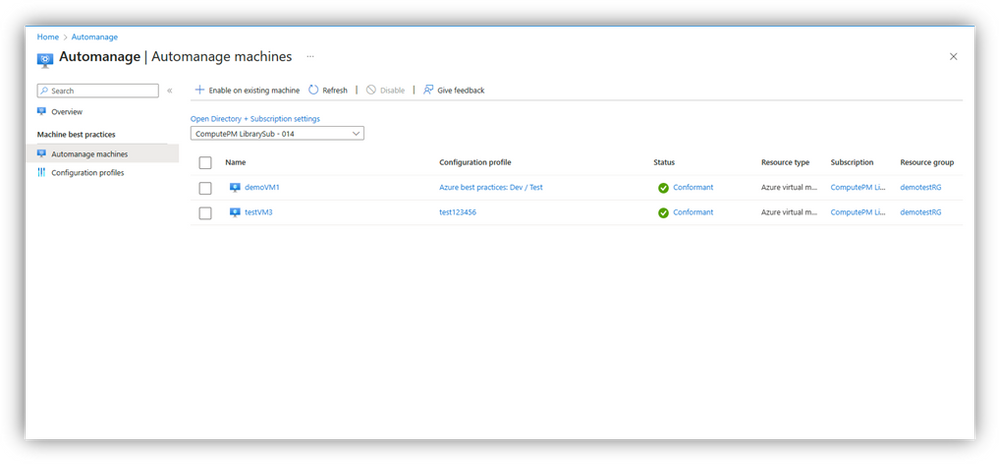
- To enable Azure Automanage for servers in Azure and Arc-enabled servers, start by browsing to the Automanage portal and click “Enable on existing machine”.
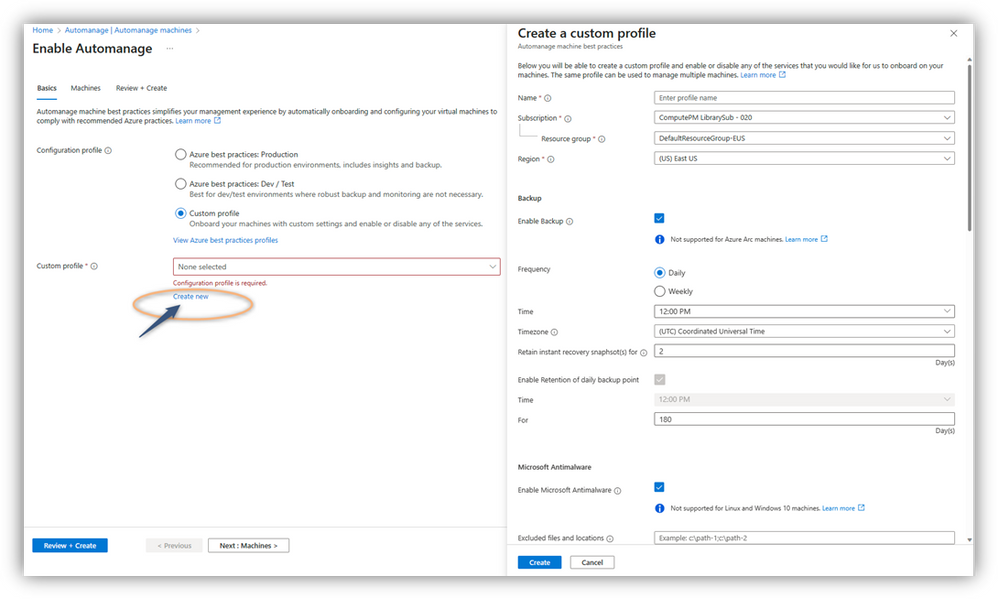
- Then create a custom configuration profile in the Configuration profile selection option.
- Enable the Machine Configuration service in the custom configuration profile and select the Assignment type/mode of your choice.
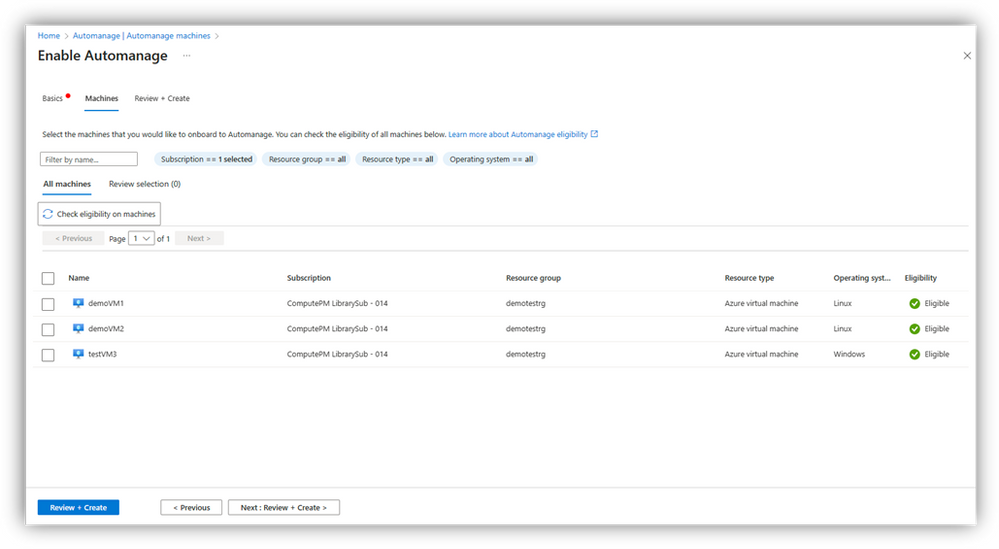
- After you choose/create your profile, select the Azure virtual machines and/or Arc-enabled servers that you want your custom profile applied to.
- Once you have selected the machines, you can click on “Review + Create”. This will initiate the Configuration profile assignment process. Automanage has now configured your machines with the best practices services. You can click on the status column to get the latest Automanage status report for your machines.
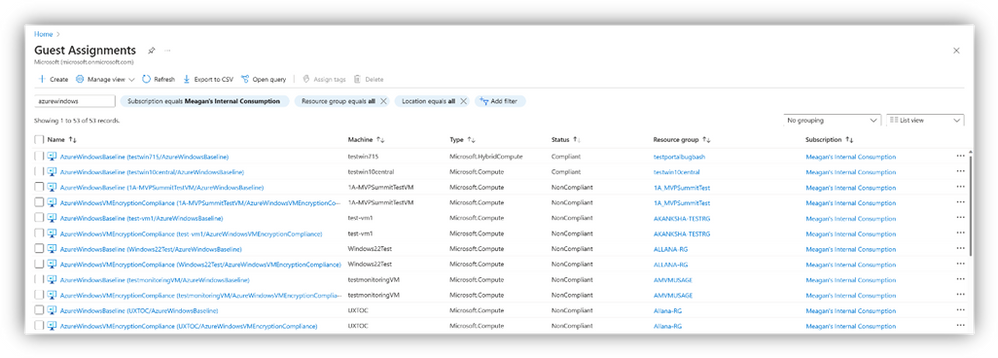
- You can query the compliance status for your entire environment using the Guest Assignments page in the Azure Portal, and through the Machine Configuration menu item within the Arc-enabled servers table of contents.
Through Guest Assignments:
Through the Guest Assignments view for Azure VMs and Arc-enabled servers, you can see all the configuration details for the selected subscriptions. At a high level, you are able to glance at the compliance across your environment.
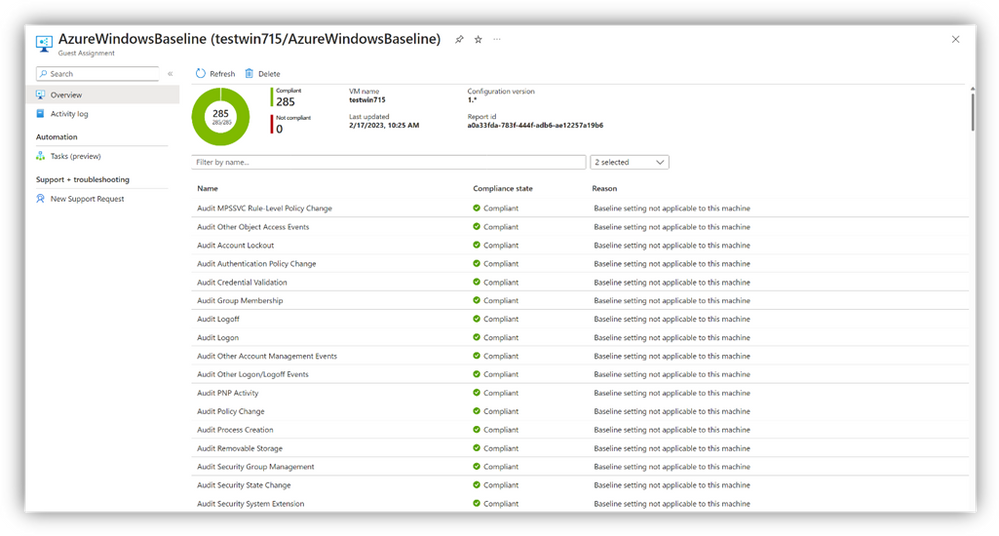
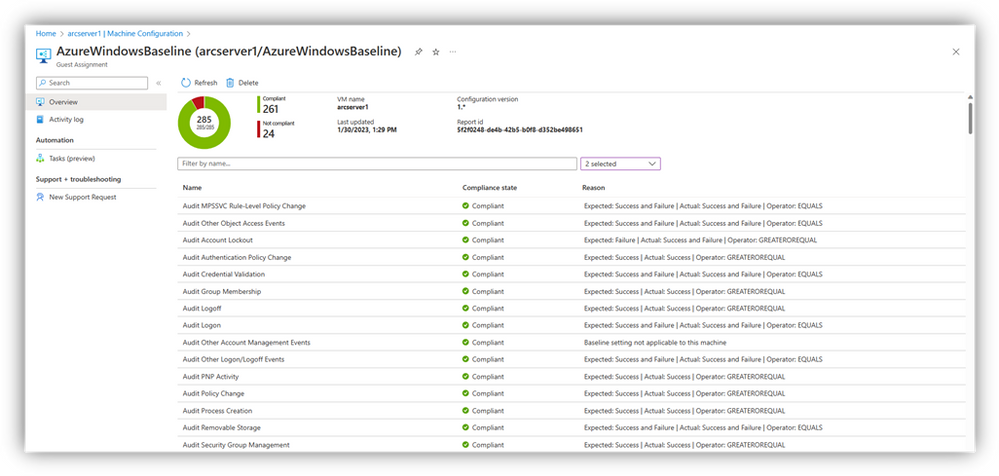
Through clicking into an individual Guest Assignment, you can see a breakdown of this compliance on a per-rule basis as well as some additional context for the reasons for non-compliance.
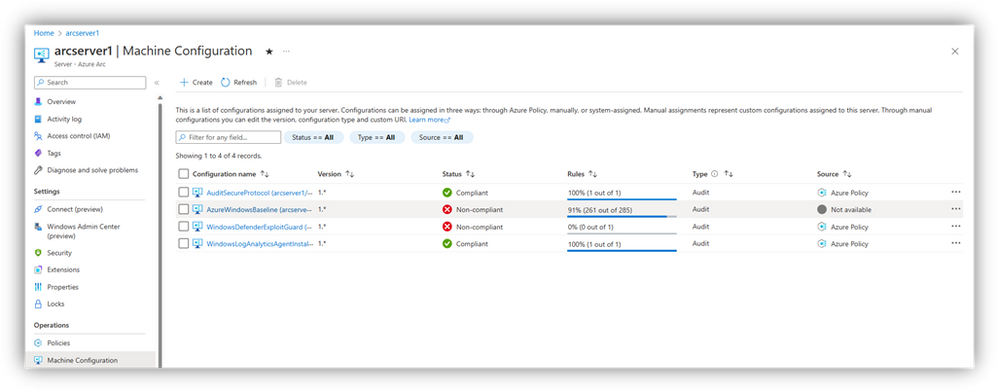
Through Arc-enabled servers Table of Contents:
This view is only for non-Azure machines – here you can see all the compliance across your Arc-enabled servers.
Clicking into an individual entry links to a Guest Assignment, showing you the breakdown of this compliance on a per-rule basis and reasons for non-compliance.
Voila! With Azure Automanage, now you can just point and click to apply CIS compliant Azure Security baselines to your environment and view its compliance.
*Note: The Windows and Linux security baselines can be applied independently of Azure Automanage. The Linux security baseline is in private preview right now.
Related Resources
To keep learning about the exciting new capabilities of Azure Automanage:
- Get started with Azure Automanage | Microsoft Azure
- Learn more about Automanage machine best practices
- Learn more about Automanage machine configuration
Published on:
Learn moreRelated posts
Setting up Power BI Version Control with Azure Dev Ops
In this blog post is a way set up version control for Power BI semantic models (and reports) using the PBIP (Power BI Project) format, Azure D...
Azure Developer CLI (azd) – March 2026: Run and Debug AI Agents Locally, GitHub Copilot Integration, & Container App Jobs
Run, invoke, and monitor AI agents locally or in Microsoft Foundry with the new azd AI agent extension commands. Plus GitHub Copilot-powered p...
Writing Azure service-related unit tests with Docker using Spring Cloud Azure
This post shows how to write Azure service-related unit tests with Docker using Spring Cloud Azure. The post Writing Azure service-related uni...
Azure SDK Release (March 2026)
Azure SDK releases every month. In this post, you find this month's highlights and release notes. The post Azure SDK Release (March 2026) appe...
Specifying client ID and secret when creating an Azure ACS principal via AppRegNew.aspx will be removed
The option to specify client ID and secret when creating Azure ACS principals will be removed. Users must adopt the system-generated client ID...
Azure Developer CLI (azd): Run and test AI agents locally with azd
New azd ai agent run and invoke commands let you start and test AI agents from your terminal—locally or in the cloud. The post Azure Developer...
Microsoft Purview compliance portal: Endpoint DLP classification support for Azure RMS–protected Office documents
Microsoft Purview Endpoint DLP will soon classify Azure RMS–protected Office documents, enabling consistent DLP policy enforcement on encrypte...
Introducing the Azure Cosmos DB Plugin for Cursor
We’re excited to announce the Cursor plugin for Azure Cosmos DB bringing AI-powered database expertise, best practices guidance, and liv...